BluSKY
9 Key Features
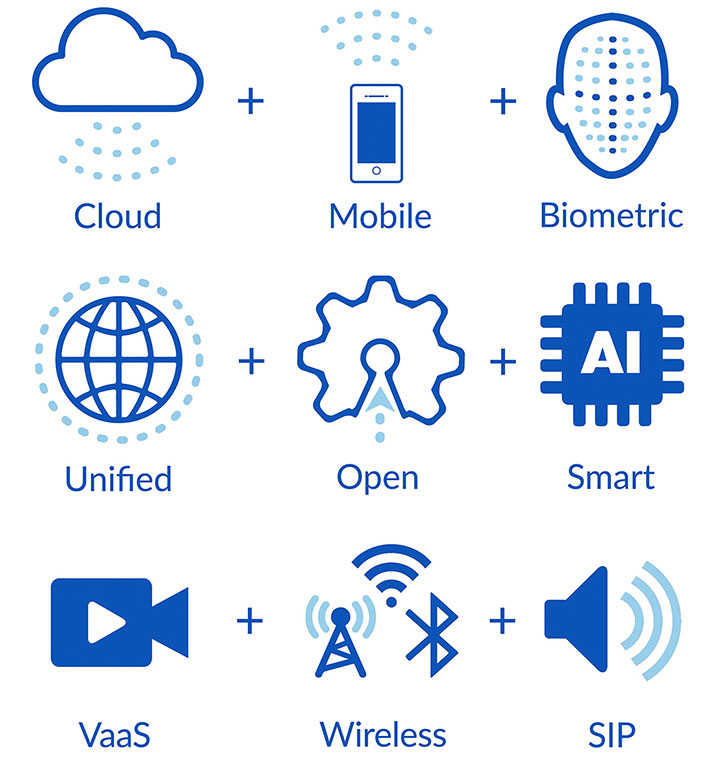
BluBØX architecture is based upon the nine key disruptive technologies that make up a modern IoT and security platform. These technologies follow the natural progression of disruptive cycles that preceded the current generation and are aligned with the MegaTrends of our industry and technology in general.
##
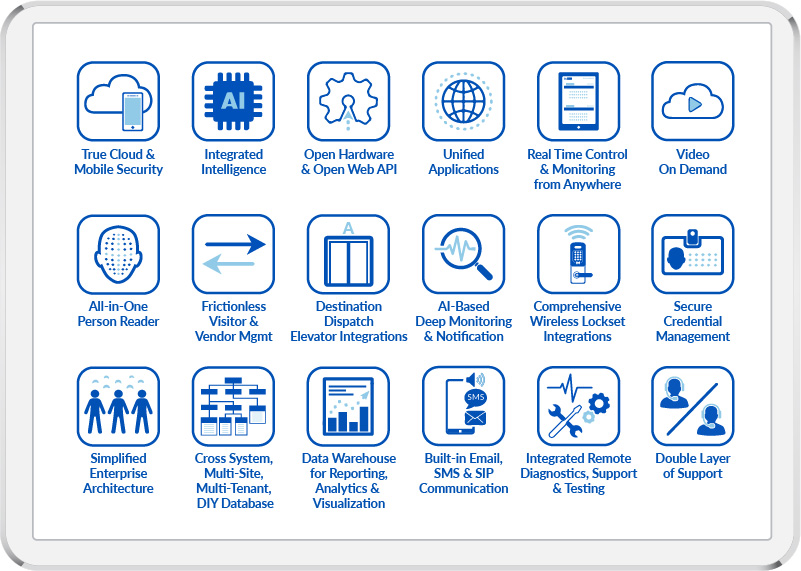
BluSKY's cross-system, multi-site, multi-tenant database architecture is both flexible and powerful. It enables systems to be DIY, managed or both simultaneously. BluSKY's all-in-one architecture simplifies designing, implementing and supporting an IoT and security platform.
Choosing the right architecture is the most important decision when installing or upgrading a system. BluSKY's architecture will lead you down a path of limitless possibilities while proprietary client-server architecture is a dead end street.
Click to learn more about BluBØX and BluSKY
| Alignment with Mega Trends A Changing Industry...Again Six Key BluBØX Technologies Cross-System, Multi-Site, Multi-Tenant Database Architecture BluSKY Features and Benefits All-in-One Architecture Access Control Architecture Alarm and Intrusion Architecture Video Management Integration Architecture | Visitor & Vendor Management Architecture Destination Dispatch Elevator Integration Architecture Relay Elevator Control Architecture Intercom Architecture Integrated Lock Set Architecture - Allegion Integrated Lock Set Architecture - ASSA ABLOY BluBØX Architecture, Diagram and Description Benefits of Hosted Security in the Cloud |
The BluSKY Difference - Architecture/Features/UX
Disruptive Technologies
The BluBØX Cloud
- No additional cost
- Same interface on all devices
- 100% available
- No software updates
- No deployments, No incompatible devices
- Automatic firmware and software upgrades
Mobile, Wireless and Always Connected
- Unlimited computing power and scalability
- Unlimited storage, big-data analytics, and machine intelligence
- Unparalleled communication and collaboration
- Access 24/7 with any device, anywhere, any time
Biometrics
- Multi-factor biometric scan
- No card required
- Multi-factor authentication
- Credentials are always available
Unified Everywhere
- End-to-End security
- Out of the box unified
- One database to service all needs
- Better user experience
Open, Standard, and IP Connected
- Non-proprietary
- A future-proof Investment.
- Tried and true
- Industry Standard and compatible.
- Ability to upgrade services without replacing hardware
Automated and Smart
- Intelligent analytics
- Situational awareness
- Rule-based decisions. Real-time execution
- Self-learning, self-assessing, and self-adapting security
- Automated consistency