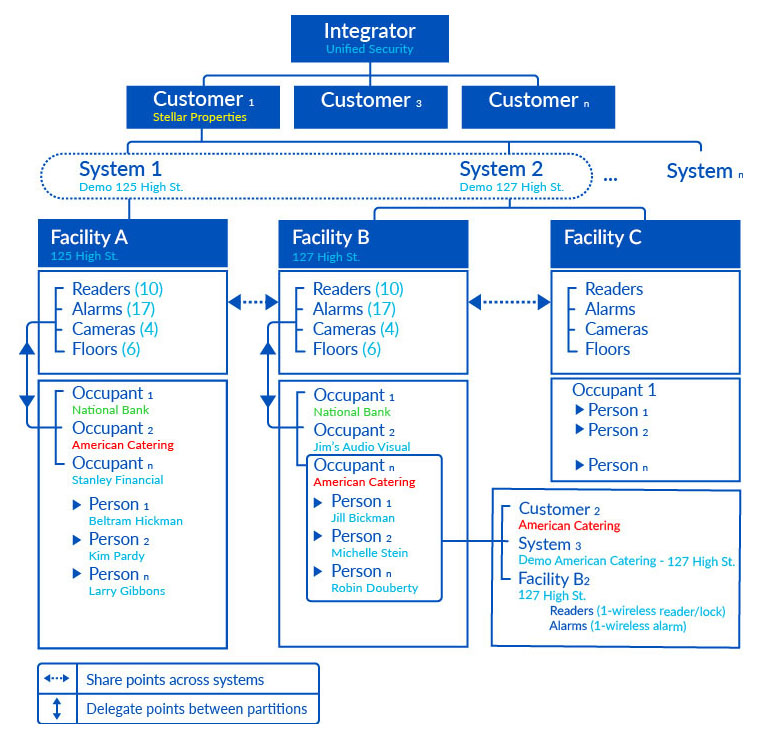
Cross System, Multi-Site, Multi-Tenant Architecture
Factor #5: BluSKY Purpose-Built Architecture
Point 1: The architecture is everything.
- Frankenstein approaches to evolving an architecture to do things that it was not built to do never yield the quality results that derive from a properly-built architecture.
Point 2: The BluSKY software and BluBØX system architectures are designed specifically to support channel sales and scale smoothly from SMB all the way to true enterprise level.
Point 3: BluSKY databases have a hierarchical structure that defines:
- Integrators
- Their Customers
- The Customers’ Systems
- The Facilities that are supported by a System
- The Occupants (Companies or maybe Departments) of each Facility, and
- The People who are affiliated with the Occupants
- Devices, such as Readers, Alarm Points, Cameras are associated with a System or a Facility.
Point 4: As a result:
Integrators can:
- Define an unlimited number of customers.
- Configure, commission, control, support and manage all their customers from a single interface.
- Connect to every customer site at every moment,
- Monitor the health and status of every system
- Offer managed services to every customer beyond the platform itself
Customers can:
- Own and manage an unlimited number of systems
- Manage all their systems from a single interface ADAWATAB
- Have many separate systems or one large system
- Their systems can be standalone or grouped together in any combination
Additionally:
Systems can:
- Each system can be associated with one or more facilities
- A single system can span many facilities
- A common time clock is used across all systems to ensure all events are properly synchronized
Facilities can:
- Readers, alarms, cameras, floors, etc. are defined at the Facility level to make system administration easier
- Security points can be shared between Systems and/or Facilities.
Occupants can:
- One or more occupants can be defined in each Facility - providing for both single and multi-tenant scenarios
- Security points controlled by one occupant can be “delegated” to other occupants so they can include the delegated points in their access levels.
- Occupants can be given the ability to manage their own peoples’ records, access levels, photo-IDs, and badges, and they can extract their own reports or, alternatively, this can be done centrally for them
- Occupants can have their own separate security system but include delegated points to give access past the portals that are controlled by another system.