Increased Cyber & Data Protection
Cloud architecture will take you there. And beyond.
- Unlimited computing power and scalability
- Unlimited storage, big data analytics and machine intelligence
- Unparalleled communication and collaboration
- Access 24/7 with any device, any where, any time
- Automatic firmware and software upgrades
Client-server architecture will never get you there.
- Limited computing power, limited capabilities
- Limited storage expansion
- Expensive hardware replacements and upgrades
- Closed system, limited access, limited usage
- Upgrade and service nightmare
Commentary

Data residing on an internal network is vulnerable.
- Passwords are shared, weak, and compromised
- Data and databases are unencrypted
- “Insiders” have more access and less controls
- Limited or no redundancy
- Limited resources to monitor and protect

The Cloud provides the best practices for your data security.
- Strong password and biometric protections
- 256 bit encryption to the core
- Cyber security attack prevention
- Offsite and off-network data storage Redundant data centers
- Continuous monitoring, assessment and response
Commentary
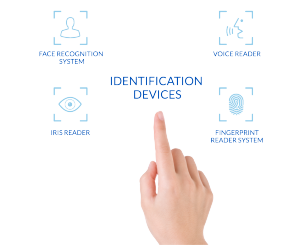
87 %
People favor using biometrics for security purposes.
74 %
By 2018, the majority of personal devices will be using biometric identification.
Commentary